Implementation of a Password Vault
Implementing a Password Vault, or Privileged Access Management (PAM), involves strategic decisions and risk mitigation. The process starts with evaluating the PAM solution’s suitability, including its functionalities, security alignment, platform choice, licensing model, and support level. Important considerations include the solution’s integration into the company's security plan, its scalability, the availability of customer support, and its high availability and failover capabilities.
Technical requirements, such as installation needs, database configuration, encryption standards, and browser compatibility, must also be addressed. Consulting and support services may be necessary, requiring a look at the consulting team's certifications and experience, and success stories from other customers.
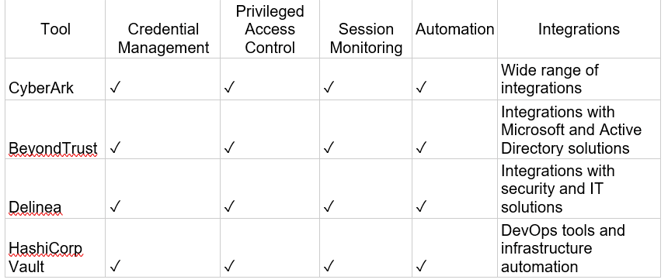
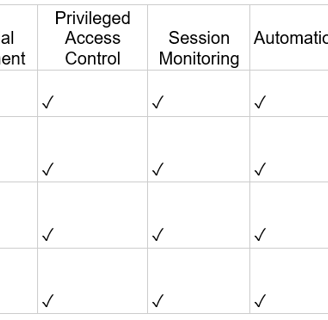
For successful implementation, a structured approach, identifying security gaps, defining the project scope, continuous communication, and the adaptation of new processes are recommended. Comparison of popular PAM tools—CyberArk, BeyondTrust, Delinea, and HashiCorp Vault—reveals differences in features, integrations, prices, and support, guiding the selection of the most suitable PAM tool based on specific needs.
Critical factors in choosing a PAM solution include essential functionalities like password and session management, ease of use, scalability, security, and compliance. The selection process involves defining requirements, comparing solutions, piloting, monitoring, and continuous improvement. Essential PAM features should cover privileged session recording, credential assessment, password generation, credential management, multi-factor authentication, and data backup.
This guide aims to provide an informative and unbiased overview to assist in the selection of a PAM solution, emphasizing the importance of aligning the choice with the organization's specific needs and context, without any commercial interest in the solutions discussed.
Implementation of a Password Vault
This article aims to provide an analysis of the technical and practical aspects to be considered when implementing a password vault project, also known as PAM ( Privileged Access Management). The intention is to assist in making strategic decisions and mitigating risks during the process.
Preliminary Considerations
1. Evaluation of the PAM Solution:
Suitability Analysis: Check whether the PAM solution meets the specific needs of the business, including functionalities, integrations and scalability.
Security Master Plan: Integrate PAM implementation into the company's PDS, ensuring alignment with existing security policies.
Platform Availability: Determine the ideal platform ( On -Premises, Cloud or SaaS) considering factors such as costs, security and technical requirements.
Features by Platform: Compare the features available on each platform to ensure you select the most suitable option.
Solution Format: Evaluate whether the solution is an Appliance or Software, considering the implications of each format in terms of installation, management and costs.
Virtual Machine Support: Verify that the PAM solution supports virtualization, enabling flexibility and scalability.
Licensing Model: Understand the solution's licensing model (per user, per device, etc. ) to optimize costs.
Source of the Solution: Evaluate whether the solution is national or international, considering aspects such as technical support, local legislation and import costs.
Customer Support: Analyze the level of support offered by the supplier, including opening hours, response time and contact channels.
High Availability and Failover : Verify that the solution offers high availability (HA) and failover capabilities to ensure system resiliency.
Load Balancing: Assess the need for load balancing to distribute traffic and optimize performance.
Impact on Warranty: Understand the implications of not following vendor recommendations for warranty and technical support.
2. Technical Requirements:
Installation Requirements: Determine the hardware requirements (OS, ROM, RAM, Processor, BD and Versions) to ensure proper installation and operation of the solution.
Database: Evaluate whether the database is stand- alone or can be externalized, considering factors such as security, performance and scalability.
Encryption Algorithms: Check the encryption algorithms used by the solution to ensure the protection of stored passwords.
Browser Compatibility: Confirm the solution's compatibility with the browsers used by the company's users.
3. Consulting and Support:
Consulting Services: Evaluate the need to hire specialized consultancy to assist in the implementation and support of the solution.
Certifications and Experience: Verify that the consulting team has certifications in the solution and experience in similar implementations.
Success Stories: Request success stories from customers who use the solution to evaluate its effectiveness and reliability.
Recommendations for Implementation:
1. Planning and Phasing:
Structured Approach: Plan and implement the project in phases to ensure a controlled process and minimize risks.
2. Needs Analysis:
Gaps and Benefits: Identify the company's security gaps and how PAM can help resolve them.
Project Scope: Define the scope of the project, including functionalities, integrations and systems to be managed.
Time and Effort Survey: Estimate the time and effort required for each phase of implementation.
3. Communication and Engagement:
Continuous Communication: Keep all stakeholders informed about the project's progress and the changes that will be implemented.
RACI table: Create a RACI matrix to define responsibilities and facilitate project tracking.
4. Adaptation to the Operating Mode:
Day-to-Day Analysis: Understand the day-to-day life of the team that will use the safe to identify and mitigate impacts on their work routine.
Creation of New Processes: Create and document new processes for using the safe, in collaboration with affected areas
5. PAM Solution Tool Comparison
This comparison looks at four popular PAM solution tools from a macro perspective. The comparison is based on criteria such as features, integrations, prices and support.
Solutions
Ø CyberArk - https://www.cyberark.com/
CyberArk is a leader in PAM, offering a wide range of robust solutions and functionality. However, consider management, cost, and support challenges before making a decision.
Leader in PAM*: Recognized as a leader by Gartner, CyberArk was the first to offer secrets management and CIEM capabilities.
Comprehensive Solutions: Offers PASM, PEDM, secret management, AAPM and CIEM solutions (through various products).
Strong points:
Broad Partner Ecosystem: Offers integrations with several existing IT tools.
Mature Products: Well-established solutions with high ratings in several areas.
Market Leader: Holds the largest market share and demonstrates consistent growth.
Continuous Innovation: Integrates with AWS and expands Just-In-Time (JIT) functionality.
Market Response: Introduces features such as transparent secret management.
Weak Points:
Complex Management and Updates: PASM software, especially the on-premises components, is challenging to manage and update.
Fragile Disaster Recovery: Relies on manual processes for failover , causing customer dissatisfaction.
High Cost: The products are among the most expensive on the market, generally requiring multiple licenses.
Unfulfilled Promises: The improvement roadmap for an old feature (PSM) remains incomplete.
Below Average Support: Customer reviews indicate below average technical support quality.
*Leading company in the Gartner Magic Quadrant
Ø BeyondTrust - https://www.beyondtrust.com/
BeyondTrust is a strong competitor in the PAM market, offering a comprehensive solution with leading functionality in specific areas such as PEDM . However, limitations in managing identity and workload secrets , concerns about the direction of the roadmap , and higher prices compared to competitors may be factors to consider when choosing.
Strong points:
Leading PAM Solution*: Recognized as a leader in the PAM market by Gartner.
Robust PASM offering: The Password Safe (PS) and Privileged Remote Access (PRA) suite offers comprehensive features in account management, session control and remote access.
Cutting-edge PEDM: Best in Class for Privilege Elevation and Delegation Management (PEDM) on UNIX/Linux and macOS , and strong performance for PEDM on Windows.
Customer focus: Highly engaged with customers, offering dedicated support and success teams.
Market Responsiveness: Continuously innovates, adding Zero Trust Network Access (ZTNA) capabilities and tools to measure PAM maturity.
Weak Points:
workload identity and secrets management : Lacks strong offerings in these areas, with limited innovation and integrations.
Roadmap Concerns : The focus appears to be shifting from core PAM enhancements like Just-In-Time (JIT) use cases to niche functionality like CIEM and password management for enterprise users.
Complex updates: Software version updates can be complex and time-consuming.
Higher Pricing: Pricing, especially for software PAM solutions, tends to be higher than the market average.
*Leading company in the Gartner Magic Quadrant
Ø Delinea - https://delinea.com/
Delinea is a leader in PAM, offering easy-to-use solutions and adopting innovative approaches. However, consider potential limitations in functionality, reliance on customization, and potential discrepancies between SaaS and on-premises options before making a decision.
Leader in PAM*: Recognized as a leader by Gartner, Delinea offers Privileged Access Management (PAM) solutions, which include Privileged Session Access Management (PASM), Device Privilege Management (PEDM), and Secret Management.
Strong points:
Consolidated Platform: Simplified PASM SaaS offerings with tiered editions, including some PEDM features.
Strong PEDM for UNIX/Linux: Stands out over PEDM for this specific operating system.
Ease of Use: Users praise Secret Server and Privilege Manager for being easy to use.
Visionary Strategy: Adopts SPIFFE and OPA standards for interoperability and centralized management.
Enhanced Sales and Support: Focused resources and expanded teams for better coverage.
Weak Points:
Limited Features: Limited functionality compared to other leaders, such as the need to install an agent on the target device for advanced RDP features.
Excessive Customization: Need for scripting through PowerShell for common configurations, which increases the burden on the client.
Discrepancy in Offerings: New features focus primarily on SaaS, potentially widening the gap between SaaS and on-premises options.
Limited Investment in R&D: Lower employee allocation dedicated to PAM R&D compared to other leading vendors.
*Leading company in the Gartner Magic Quadrant
Ø HashiCorp Vault - https://www.hashicorp.com/
HashiCorp is a strong player in secrets management, but is new to PAM . While Vault stands out in its category, Boundary faces feature gaps compared to established PAM solutions. Consider the high cost, unique pricing model, and potential focus misalignment before choosing HashiCorp for PAM.
Strong points:
Leader in Secrets Management: Holds the largest market share for independent solutions and receives high reviews for its Vault product .
Strong Marketing and Training: Demonstrates brand awareness and offers excellent resources for self-learning.
Positive Customer Experience: Users appreciate Vault 's encryption and ease of integration.
Weak Points:
PAM newcomer: Boundary lacks features present in more mature products, such as privileged account lifecycle management, discovery, and credential management . Its session management is also below average.
High Cost: Customers find Vault expensive, and Boundary 's unique "sessions per month" pricing model is unusual and potentially disadvantageous.
Recent Layoffs: Workforce reductions raise concerns about stability and support.
Limited Market Focus: The maturity model prioritizes DevOps and cloud-based use cases over traditional enterprise environments.
Source: https://www.gartner.com/doc/reprints?id=1-2EYAFT0R&ct=230911&st=sb
6. Recommendation
Choosing the ideal PAM tool depends on your company's specific needs. It is important to consider the criteria mentioned in this comparison, such as features, integrations, prices and support, to make an informed decision.
Critical factors :
· Essential functionalities: password and session management, monitoring, JIT access control, privilege delegation, integration with other systems.
· Ease of use and implementation: friendly interface, quick implementation, efficient technical support.
· Scalability and flexibility: ability to handle growth, support for different platforms, customization.
· Security and compliance: Strong encryption, compliance with security standards, frequent updates.
Selection process :
· Define requirements: assess risks, identify accounts and systems to protect, define essential resources.
· Search and compare solutions: analyze available solutions, compare features, prices and support.
· Implement and pilot: implement in a test environment, perform tests and simulations, train administrators and users.
· Monitor and improve: monitor performance, identify areas for improvement, stay up to date, perform audits.
In addition to these recommendations, here are some essential features that a PAM solution should have:
· Monitoring and Recording Privileged Sessions: Record all activities carried out by privileged accounts.
· Assessment of Privileged Credentials: Regularly check the security of passwords and credentials.
· Native Strong Password Generator: Have a feature to create strong passwords.
· Credentials and Key Management: Centrally manage credentials and access keys.
· Multi-Factor Authentication : Strengthen security with additional authentication.
· Data Backup : Ensure data availability and recovery in case of failures.
References
https://www.gartner.com/doc/reprints?id=1-2EYAFT0R&ct=230911&st=sb
https://www.gartner.com/reviews/market/privileged-access-management
Important :This article is not intended to advertise, benefit or disparage any specific PAM (Privileged Access Management) solution.The intention is solely to provide an informative and impartial guide to assist in choosing or better understanding a PAM solution.By presenting the characteristics and functionalities of different solutions, I do not seek to influence your purchasing decision, but rather to offer a comprehensive overview of the market and available resources.I believe that choosing the ideal PAM solution should be made based on a careful analysis of your specific needs and the context of your organization.This article aims to be a starting point for this analysis, offering valuable information so that you can make an informed and appropriate decision.I emphasize that I have no commercial interest in any of the solutions mentioned in this article.The goal is to provide relevant, quality information so you can make the best decisions for your organization.


Author: Tchule Ribeiro is a distinguished cybersecurity professional with more than two decades of experience in the information technology domain. He has carved out a niche for himself as a seasoned leader in both cybersecurity and infrastructure management. Throughout his extensive career, Ribeiro has traversed a variety of dynamic industries, making significant contributions particularly in the finance and civil engineering sectors. Moreover, his expertise has been instrumental in the pharmaceutical and construction fields. Ribeiro's academic background lays a robust foundation for his professional endeavors, commencing with a Bachelor of Science in Computer Science, followed by an MBA in Computer Network Project Management, and further enhanced by qualifications in network technology and electronics. A passionate advocate for continuous learning and collaboration, Ribeiro is always eager to engage in discussions related to cybersecurity and infrastructure management, seeking opportunities to share his comprehensive experience and insights.


